In today’s digital world, mobile numbers are directly linked to banking, social media, and authentication systems. This makes them a key target for cybercriminals.
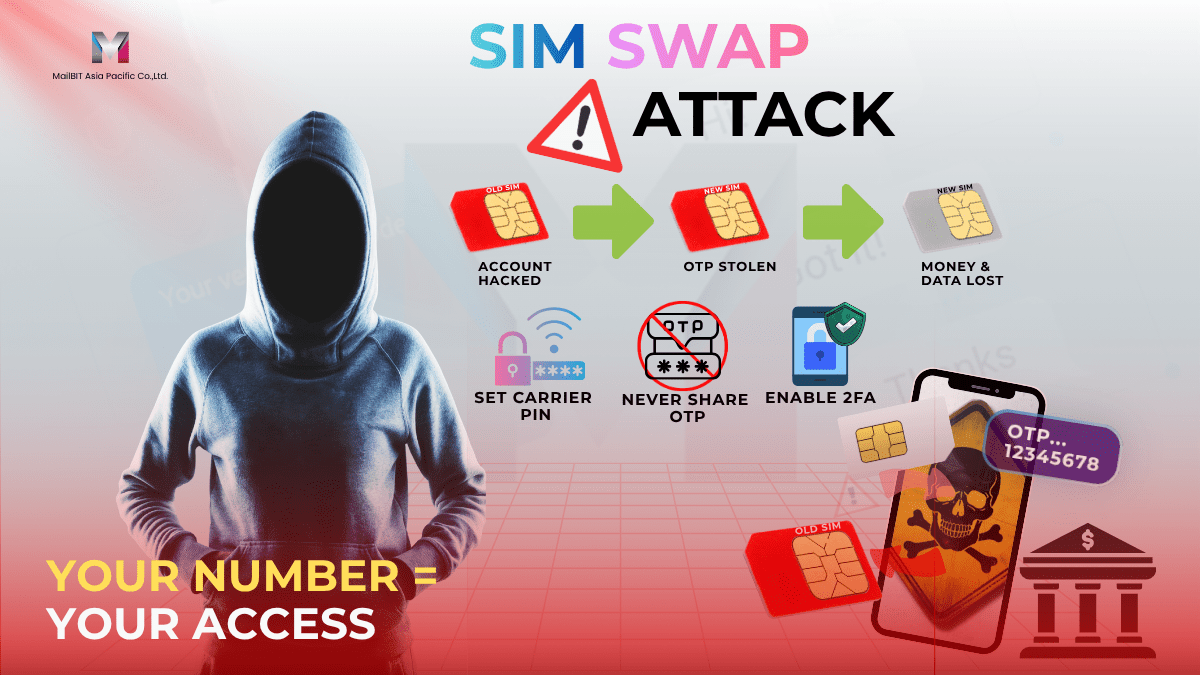
One of the most serious threats is SIM Swap fraud, a cyberattack that allows hackers to take control of a victim’s phone number and gain access to sensitive accounts.
Businesses that rely on OTP SMS, SMS authentication, and secure messaging systems must understand how SIM swap attacks work and how to prevent them.
To improve protection, explore secure SMS solutions and enterprise messaging platforms designed for modern businesses.
What is SIM Swap?
SIM Swap (or SIM swapping attack) is a type of fraud where an attacker transfers your phone number to a new SIM card under their control.
Once successful, the attacker can receive:
- OTP (One-Time Password) codes
- Banking alerts
- Account verification messages
- Password reset requests
This allows them to bypass security systems and gain access to critical accounts.
To prevent this risk, businesses should adopt advanced SMS security solutions and OTP SMS protection systems.
How SIM Swap Attacks Work
SIM swap attacks typically involve social engineering. Attackers gather personal information and impersonate the victim to request a SIM replacement.
Steps include:
- Collecting personal data from phishing or data leaks
- Contacting telecom providers
- Requesting SIM replacement
- Intercepting OTP SMS messages
This highlights the importance of using real-time SMS monitoring tools and secure A2P messaging platforms.
Risks of SIM Swap Attacks
💳 Financial Fraud
Unauthorized transactions can occur through compromised accounts.
🔐 Account Takeover
Attackers can gain access to email, banking, and business systems.
📉 Brand Reputation Damage
Loss of trust can significantly impact business credibility.
🧾 Data Breach
Sensitive information may be exposed.
To mitigate these risks, companies should implement business SMS security platforms and enterprise SMS gateway solutions.
Why SIM Swap is Dangerous for OTP SMS
Many businesses depend on OTP SMS authentication for security. However, SIM swap attacks allow attackers to intercept OTP codes.
To enhance security, organizations should use secure OTP SMS services and cloud messaging solutions.
How to Prevent SIM Swap Attacks
🔒 Set a Carrier PIN
Add a PIN to protect your mobile account.
📵 Never Share OTP
Keep OTP codes confidential at all times.
👀 Monitor Signal Loss
Unexpected signal loss may indicate SIM swap activity.
📲 Enable Multi-Factor Authentication
Use additional authentication layers beyond SMS.
🛡 Use Secure Messaging Infrastructure
Partner with providers offering trusted SMS gateway services and secure business SMS platforms.
Best Practices for Businesses
To reduce SIM swap risks, businesses should:
- Use multi-layer authentication
- Monitor suspicious activity
- Implement fraud detection systems
- Educate customers on cybersecurity
- Choose enterprise SMS communication platforms
A strong A2P messaging infrastructure ensures better protection and reliability.
Conclusion
SIM swap attacks are a growing cybersecurity threat that can lead to financial loss, account takeover, and data breaches.
Businesses that rely on SMS communication must invest in secure messaging infrastructure, OTP protection systems, and trusted SMS providers.
To strengthen your business security, explore advanced SMS gateway solutions, real-time SMS analytics tools, and enterprise messaging services.
📱 LINE: @MailBIT
📞 Tel: +66 2-237-7778 | +66 81-300-0958 (Bangkok, Thailand)
#SIMSwap #SMSFraud #CyberSecurity #OTPSecurity #SMSGateway #A2PMessaging #BusinessSMS #DigitalSecurity #FraudPrevention #CloudMessaging #MailBIT
 English
English  ไทย
ไทย